Website malware is no longer a minor technical fault, it is a business emergency that compromises data, disrupts operations, damages reputation, and impacts revenue. An infected website can silently spread ransomware, steal user information, manipulate traffic, inject scam pages, redirect visitors, and trigger trust warnings on browsers. Many organisations only discover infections after serious damage: search engines blacklisting their domain, clients lose confidence, or internal systems become compromised.
The most efficient protection begins long before an attack happens, which is why a secure website development service plays a key role in prevention, threat reduction, and faster recovery. Malware recovery is not simply file deletion; it requires identifying attack origins, verifying backups, cleaning infected assets, securing entry points, monitoring anomalies, and rebuilding structural weaknesses. Without a forensic-level investigation, malware almost always returns stronger and more disruptive.
How Malware Impacts a Business Beyond the Website
Malware consequences extend far beyond broken pages or slow performance. Infections disrupt lead generation, affect customer data integrity, interrupt automated processes, and expose organisations to compliance risk and financial loss. Many companies continue operating without detecting infection, unknowingly leaking user data or serving malicious scripts to visitors. Depending on severity, industries with data compliance obligations may also face regulatory investigations, financial penalties or operational restrictions during cleanup phases.
Loss of Customer Trust
Browser warnings like “dangerous site” or “data breach detected” cause immediate drop-offs. Even after malware is removed, rebuilding credibility takes longer than technical recovery. Customers rarely return to brands that compromise safety.
Revenue and Conversion Decline
Malware interrupts forms, payment pages, emails, booking systems, and automation flows. Visitors may bounce due to redirects, page failures, or risk warnings, turning functioning traffic into lost revenue without immediate visibility.
SEO and Visibility Damage
Search engines penalise infected domains quickly, removing indexed pages, lowering visibility, and restricting organic reach. Recovery is slow, and some sites never regain previous ranking authority even after a complete cleanup.
Common Entry Points of Website Malware
Most infections enter through outdated software, insecure configurations, compromised credentials, and unprotected server environments. Attackers no longer focus only on large institutions, automated malware bots scan thousands of small and medium sites looking for easy entry points. Many infections remain hidden by embedding in database fields, encrypted files, backup archives, third-party scripts, or dormant admin accounts, making detection difficult without deep-level forensic tracing.
Weak or Stolen Login Access
Phished or reused passwords allow hackers direct admin entry. Once inside, attackers create fake accounts, embed payload scripts, modify core files, or plant hidden backdoors for future remote access.
Poorly Maintained Plugins
Outdated or unverified plugins often contain vulnerabilities. These extensions become attack tunnels that grant unauthorised access, allowing malware injections without visible disruptions to the frontend.
Unprotected Server Configurations
Shared hosting or weak file permissions can enable cross-site contamination. Malware spreads across directories, modifies root files, and embeds persistence scripts that survive routine cleanups.
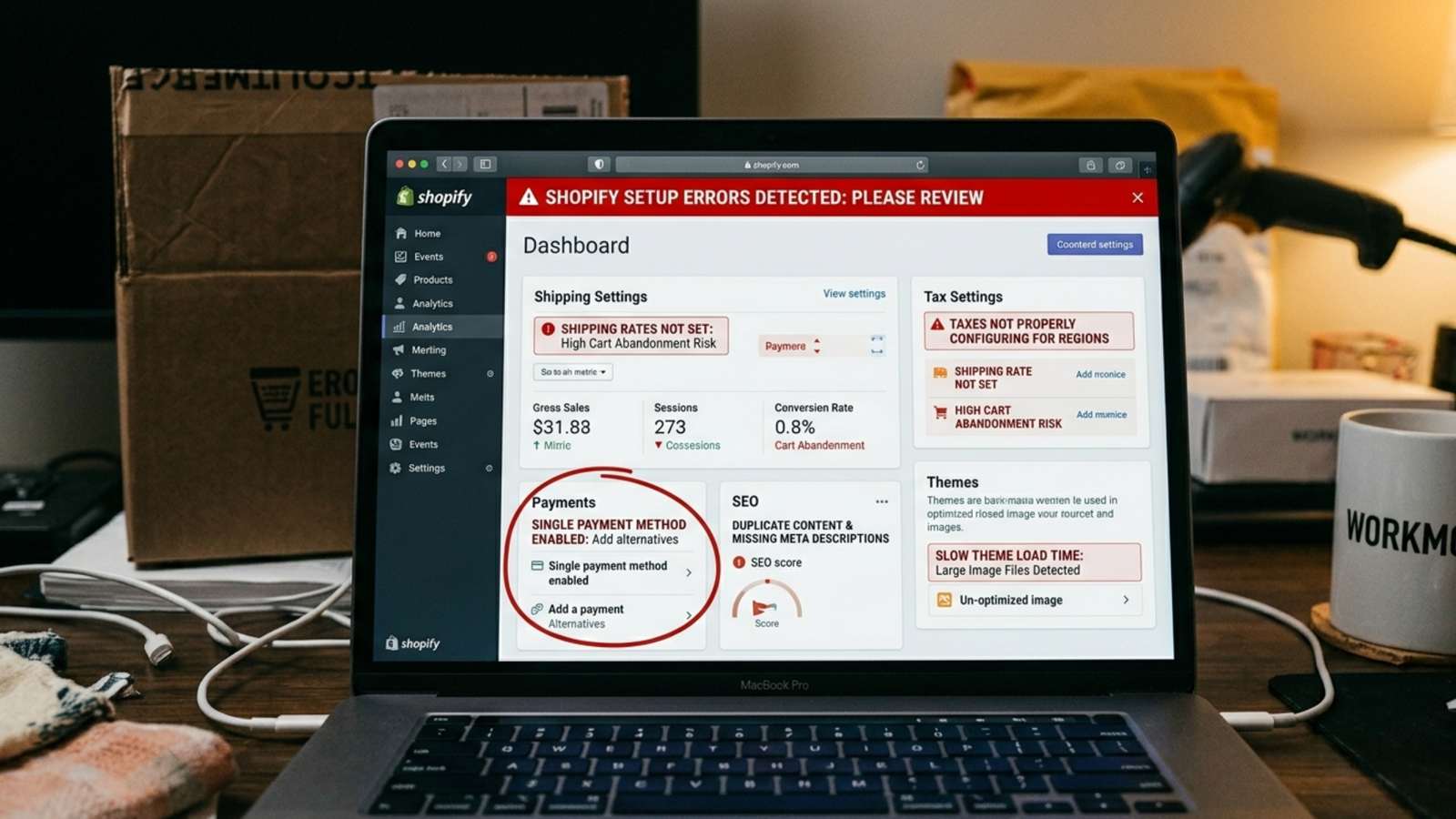
Early Warning Signs Most Teams Overlook
Malware frequently appears silent before causing major damage. Owners often notice symptoms only after users report warnings or hosting providers issue alerts. However, subtle early signals always exist, spike in server requests, unknown admin accounts, random file changes, traffic from unusual regions, slow backend response, failing cron jobs, or unexpected email activity. Small abnormalities can indicate infection long before visible damage appears.
Sudden Performance Irregularities
Unexplained slow loading, high CPU usage, sudden downtime, database lag, or backend delays often indicate hidden scripts, encryption abuse, traffic manipulation, or server resource hijacking by malware processes.
Unauthorised Backend Changes
New admin users, unknown database tables, modified timestamps, unfamiliar scripts, or disabled security plugins often indicate unauthorised access rather than a technical malfunction.
Immediate Actions After Detecting Malware
Once malware is suspected, response speed matters, but response quality matters more. Removing files without investigation risks permanent reinfection. Effective recovery requires isolation, forensic tracing, backup validation, credential resets, server audits, and controlled restoration. Cleanup must eliminate infection AND close the door it entered through; otherwise, reinfection cycles continue aggressively.
Take the Website Offline Safely
Disconnect traffic without deleting data. This prevents infection spread, protects visitor devices, stops malware execution, and allows investigators to analyse the breach in controlled conditions.
Identify the Infection Source
Before deleting anything, trace how malware entered and where it spread. Without root cause detection, removal becomes temporary, and attackers often regain access through the same vulnerability.
Deep Cleaning vs Temporary Fixes
True malware recovery removes infection from files, servers, databases, scripts, backups, authentication layers, and connected systems. Superficial cleaning often misses encoded database injections, dormant scripts, or secondary backdoors. Real remediation requires integrity verification, file validation, checksum comparison, server rule rebuilding, and secure redeployment.
Remove Hidden Payloads
Malware hides in uploads, SQL tables, themes, log files, backup archives, and encrypted fragments. Deletion must target infected code, execution triggers, and regeneration scripts — not just visible symptoms.
Clean and Validate Databases
Injected malware in database fields can recreate the infection even after files are cleaned. Tables must be scanned, sanitised, and validated individually to ensure safe restoration.
Why Professional Security Support Matters
Cyberattacks have evolved beyond manual fixes. Businesses require structured remediation, threat monitoring, infrastructure audits, and intrusion blocking from security specialists. Expert intervention ensures infections are traced to their origin and removed safely without breaking functionality, corrupting data, or leaving hidden reinfection points. This reduces downtime, protects digital assets, and prevents repetition.
Enterprise-Level Threat Removal
Professional Cybersecurity Services perform penetration scanning, heuristic malware detection, behavioural analytics, intrusion prevention, firewall deployment, and proactive server hardening to eliminate infections at source.
Building Security Into Development
Security cannot be added at the end, it must be engineered into every system layer, integration, and user interaction model. Secure architecture includes data encryption, access rotation, secure API communication, intrusion detection, monitored admin logs, structured deployments, and vulnerability testing. Websites built without security planning become predictable targets, regardless of size or industry.
Secure Website Design Frameworks
A reliable web design service ensures secure design components, protected front-end execution, controlled admin pathways, form-level encryption and browser-safe interaction standards to block common exploit vectors.
Securing Customer Data and CRM Ecosystems
Modern websites connect to customer journeys, pipelines, support automation and digital communication records. When these connections lack secure logic, breaches expand beyond the website into customer databases and internal workflows. CRM environments need encrypted storage, regulated access layers, and tamper-proof data transmission to remain resilient against cyber compromise.
CRM Security as a Defence Layer
A secure crm development service protects customer ecosystems through encrypted data flow, role-based access, secure API exchange, storage isolation, automated threat flags, and monitored behavioural anomalies.
Why Regional Expertise Makes a Difference
Cyber compliance requirements vary by country, industry, and legal framework. Infrastructure, hosting rules, data governance, and digital security expectations differ across markets, making local expertise essential for regulatory alignment and faster recovery cycles.
Compliance-Aware Recovery Standards
Collaborating with a trusted website developer in the UAE ensures systems align with local governance models, data protection expectations, digital compliance frameworks, and operational security benchmarks.
Long-Term Protection Framework
A recovered website requires continuous monitoring rather than one-time fixes. Effective defence includes firewalls, automated patching, log monitoring, vulnerability scanning, bot filtering, encrypted access, permission restructuring, and anomaly tracking.
Continuous Monitoring Systems
Security should detect threats before execution. Real-time activity logs, behavioural alert,s and automated blocking systems minimise exposure and drastically reduce potential impact.
Structured Access Control
Permission models must restrict admin privileges, enforce multi-factor authentication, regulate access logs, and lock unauthorised execution to prevent credential-based breaches.
FAQs
Q1: Can plugins remove malware completely?
Not always. Plugins catch common malware, but advanced infections can hide in databases, server files, or backdoors, which need manual investigation and deeper security cleanup.
Q2: Is restoring a backup safe after malware?
Only if the backup is scanned first. Some backups already contain malware, so restoring without checking can reinfect the website.
Q3: How long does malware recovery take?
It depends on the damage. Some infections are fixed in 1–3 days, while deeper server or database infections can take weeks to clean and secure properly.
Q4: Can malware permanently affect SEO?
Yes. If malware stays active for long time, search engines may blacklist or deindex the site, and full ranking recovery can take months even after cleanup.
Q5: What prevents reinfection?
Fixing vulnerabilities, resetting access, adding security layers, monitoring threats and keeping software updated helps prevent repeat attacks and keeps the site protected.
Conclusion
Recovering from malware is far more than deleting infected files, it is a complete restoration of security, operational stability, user trust, and digital resilience. Websites that recover successfully do more than clean the infection; they restructure access points, rebuild defensive layers, and enforce long-term monitoring to prevent future compromises. With security strategies supported by Qudratx Taqniya, recovery becomes a structured process focused on durability, intelligence, and continuous risk prevention rather than temporary fixes. True protection means evolving from reaction mode into proactive defence, ensuring the website remains safe, reliable, and future-ready.